Here’s why passkeys are today’s most secure authentication option.
Passkeys are a powerful authentication method with the potential to take passwordless authentication to new heights. Users can look forward to a future in which the vulnerabilities and complexities associated with traditional username and password-based authentication systems are greatly reduced – and potentially eliminated altogether.
By leveraging public-key cryptography, biometrics, and device attestation, passkeys enable users to securely authenticate themselves across various devices and platforms with a simple touch, face scan, or by entering a PIN code.
How Does Authentication With Passkeys Work?
Passkeys provide a secure, convenient authentication method that not only gets rid of the need for passwords, but also significantly reduces the risk of password theft and phishing attacks. Passkeys are an implementation of the FIDO2 standard, which covers two main user flows: Authenticator registration and user authentication.
Authenticator Registration
When a user decides to opt in to authentication using passkeys, they need to register their device, such as a laptop or mobile device, with the service provider. This device then becomes their authenticator device, which is otherwise known as the authenticator. During the registration process, the authenticator generates a unique set of cryptographic login credentials, also known as keys. The user’s private key remains securely stored in an authenticator, while the public key is registered with the service provider.
Some FIDO2 authenticators take security a step further by supporting biometric authentication, such as fingerprint or facial authentication, or alternatively, a PIN code to bolster the protection of the private key.
Furthermore, there are two main categories of authenticators available: Platform and cross-platform. Platform authenticators are built directly into a main device — think TouchID on Mac or Windows Hello — while cross-platform authenticators are portable devices that can be connected to the main device via USB, Bluetooth, or NFC.

User Authentication
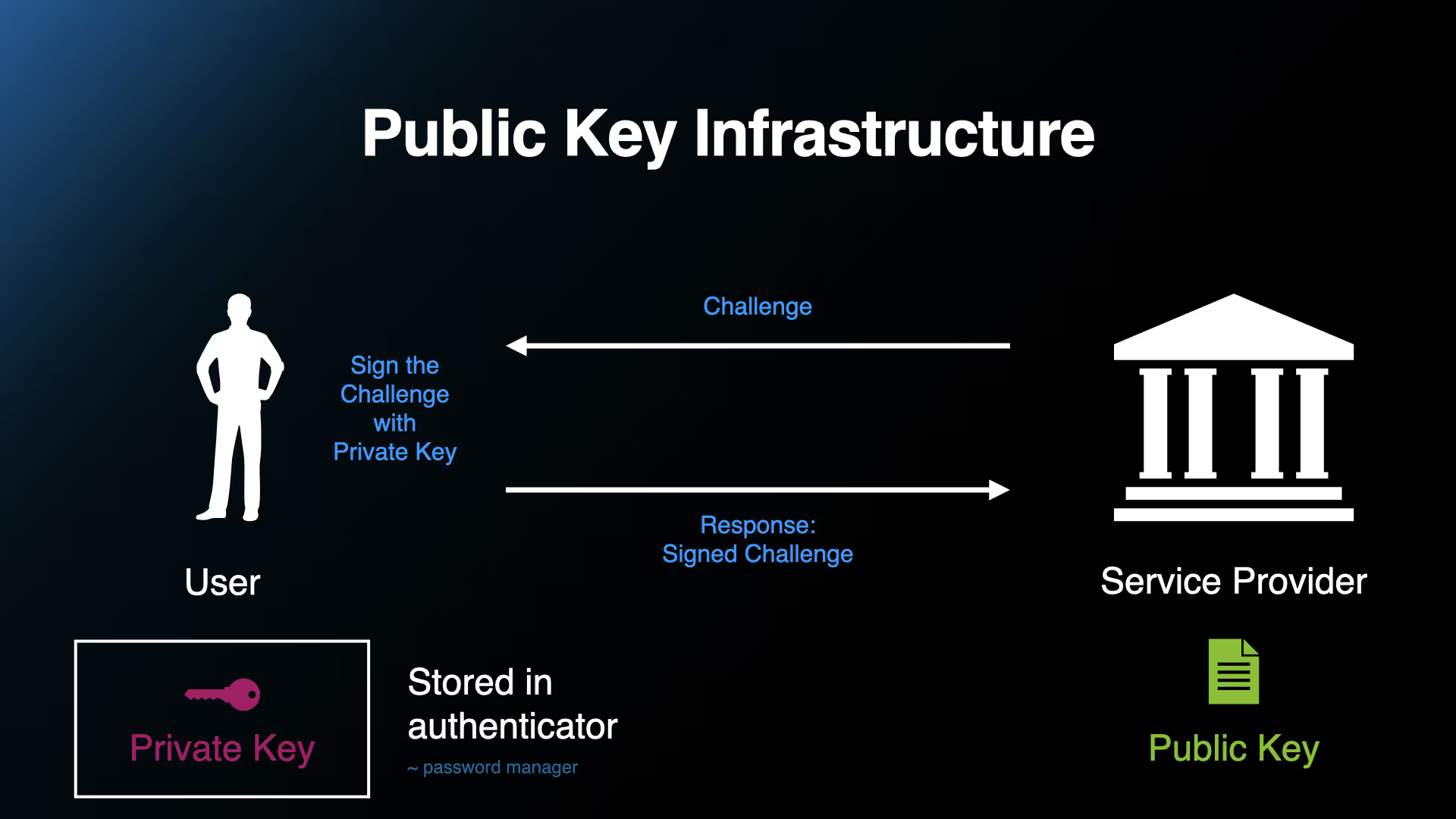
Once the user has registered the FIDO2 authenticator and is ready to log in, the following steps are carried out:
- The service provider generates a random challenge to prove the user’s identity
- The user makes use of an authenticator to sign the challenge using their private key
- The user sends the signed challenge back to the service provider, and in doing so, delivers secure proof of their identity
This entire process is built into the operating system and web browser, and as a result, the process is standardized and resilient against various digital attacks.
Benefits of Implementing Authentication With Passkeys
Among the myriad benefits of implementing passkeys for banks and fintech companies, there are several that especially stand out:
- No app or mobile device needed:
As passkeys work on any modern device and are built directly into operating systems and web browsers, it isn’t necessary to use a dedicated mobile app to carry out authentication. As a result, passkeys are easy to deploy and roll out.
- User experience:
A convenient, user-friendly experience is at the core of authentication with passkeys, which makes it possible for users to select their preferred secure, passwordless authentication on the device or platform of their choice.
- Resistance to phishing attacks:
Since passkeys are built into a web browser and cryptographic keys are unique for each website, the web browser only offers the appropriate key for the corresponding website. The security policies built into the web browser prevent phishing sites from triggering the passkey authentication flow intended for the legitimate site.
- Data breach prevention:
The private key never leaves a user’s authenticator device, nor is it ever stored on a server. As only public keys are stored on the server, passkeys greatly reduce the risk of a sensitive data leak from taking place.
- Security and PSD2 compliance:
Passkeys fulfill the Strong Customer Authentication (SCA) requirements of PSD2 regulation by providing a secure, multi-factor authentication method.
By making it possible for password-based logins to be replaced with secure, passwordless experiences across websites and apps, passkeys have undoubtedly become today’s most secure authentication option.
In our next blog post, we’ll be diving into the roles of the technical specifications associated with passkeys and the FIDO2 standard. Stay tuned!
The Origins of FIDO2
FIDO2’s creators are the FIDO ("Fast Identity Online") Alliance. For more than a decade, the FIDO Alliance has been home to a collection of the brightest minds in the technology and security industry. Since its founding in 2012 and public launch in early 2013, the organization has remained focused on providing open, free authentication standards in order to help reduce the world's reliance on passwords. The Alliance’s initial deployment of FIDO authentication, which is described as “the answer to the global password problem”, took place in early 2014.
In February 2016, the World Wide Web Consortium (W3C) launched a new standards effort based on web APIs submitted by the FIDO Alliance known as FIDO2. In this initiative, it was the FIDO Alliance’s goal to work together with the W3C to standardize FIDO strong authentication across all web browsers and related web platforms.


.webp)