Products
Complete Product Name
lorem ipsum dolor sit amet, consectetur adipisicing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua

Great to Use
Your customers will love the passwordless experience provided by our solutions.
Quantum-resistant
Under the hood, we use post-quantum cryptography endorsed by NIST.
Lorem ipsum dolor sit amet, consectetur adipisicing elit sed do eiusmod tempor.
Comply with regulations
Policy controls, step-up flows, and evidence generation to support PSD3/PSR SCA requirements and audits.
Reduce account takeover
Bind a user to a mobile device using cryptographic keys stored in platform security (e.g., TEE/SE/Keychain).
Improve user experience
Fast login and payment approvals, convenient biometric authentication, secure PIN code.
Audit and observability
Evidence-rich logs, export capabilities, and monitoring hooks for SIEM/SOC workflows.
Multi-factor authentication
Device biometrics (Face ID) and PIN, device possession, and fallback methods designed for inclusivity and resilience.
Policy-driven authentication
Adaptive rules: step-up, risk thresholds, factor constraints, channel restrictions, and user journeys.
Secure device binding
Prevent common OTP/push weaknesses with device binding, signed approvals, and contextual checks.
Social attack resistance
Mitigate OTP interception, SIM swap exposure, overlay attacks, and social engineering patterns.
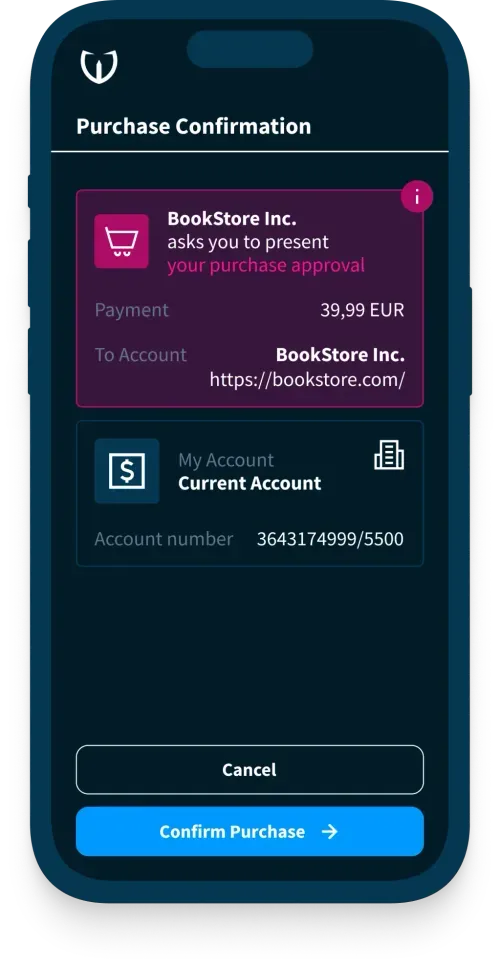
Transaction and login approvals
Approve logins and high-risk actions with signed messages and clear user context (who/what/where).
Trusted by leading financial organizations




Benefits
Highlighted section with an interesting information and a link
Great to Use
Your customers will love the passwordless experience provided by our solutions.
Quantum-resistant
Under the hood, we use post-quantum cryptography endorsed by NIST.
Lorem ipsum dolor sit amet, consectetur adipisicing elit sed do eiusmod tempor.

Comply with regulations
Policy controls, step-up flows, and evidence generation to support PSD3/PSR SCA requirements and audits.

Reduce account takeover
Bind a user to a mobile device using cryptographic keys stored in platform security (e.g., TEE/SE/Keychain).

Improve user experience
Fast login and payment approvals, convenient biometric authentication, secure PIN code.
Audit and observability
Evidence-rich logs, export capabilities, and monitoring hooks for SIEM/SOC workflows.
Multi-factor authentication
Device biometrics (Face ID) and PIN, device possession, and fallback methods designed for inclusivity and resilience.
Policy-driven authentication
Adaptive rules: step-up, risk thresholds, factor constraints, channel restrictions, and user journeys.
Secure device binding
Prevent common OTP/push weaknesses with device binding, signed approvals, and contextual checks.
Social attack resistance
Mitigate OTP interception, SIM swap exposure, overlay attacks, and social engineering patterns.
Transaction and login approvals
Approve logins and high-risk actions with signed messages and clear user context (who/what/where).
Use Cases
Use case tagline, 1 or 2 lines
Lorem ipsum dolor sit amet, consectetur adipisicing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua.

Description of the 1st Product Capability
Lorem ipsum dolor sit amet, consectetur adipisicing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua.
- Out-of-band and assisted activation options
- Device change and re-enrollment scenarios
- Recovery flows that balance security and support cost

Description of the 2nd Product Capability
Lorem ipsum dolor sit amet, consectetur adipisicing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua.
- Out-of-band and assisted activation options
- Device change and re-enrollment scenarios
- Recovery flows that balance security and support cost

Description of the 3rd Product Capability
Lorem ipsum dolor sit amet, consectetur adipisicing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua.
- Out-of-band and assisted activation options
- Device change and re-enrollment scenarios
- Recovery flows that balance security and support cost
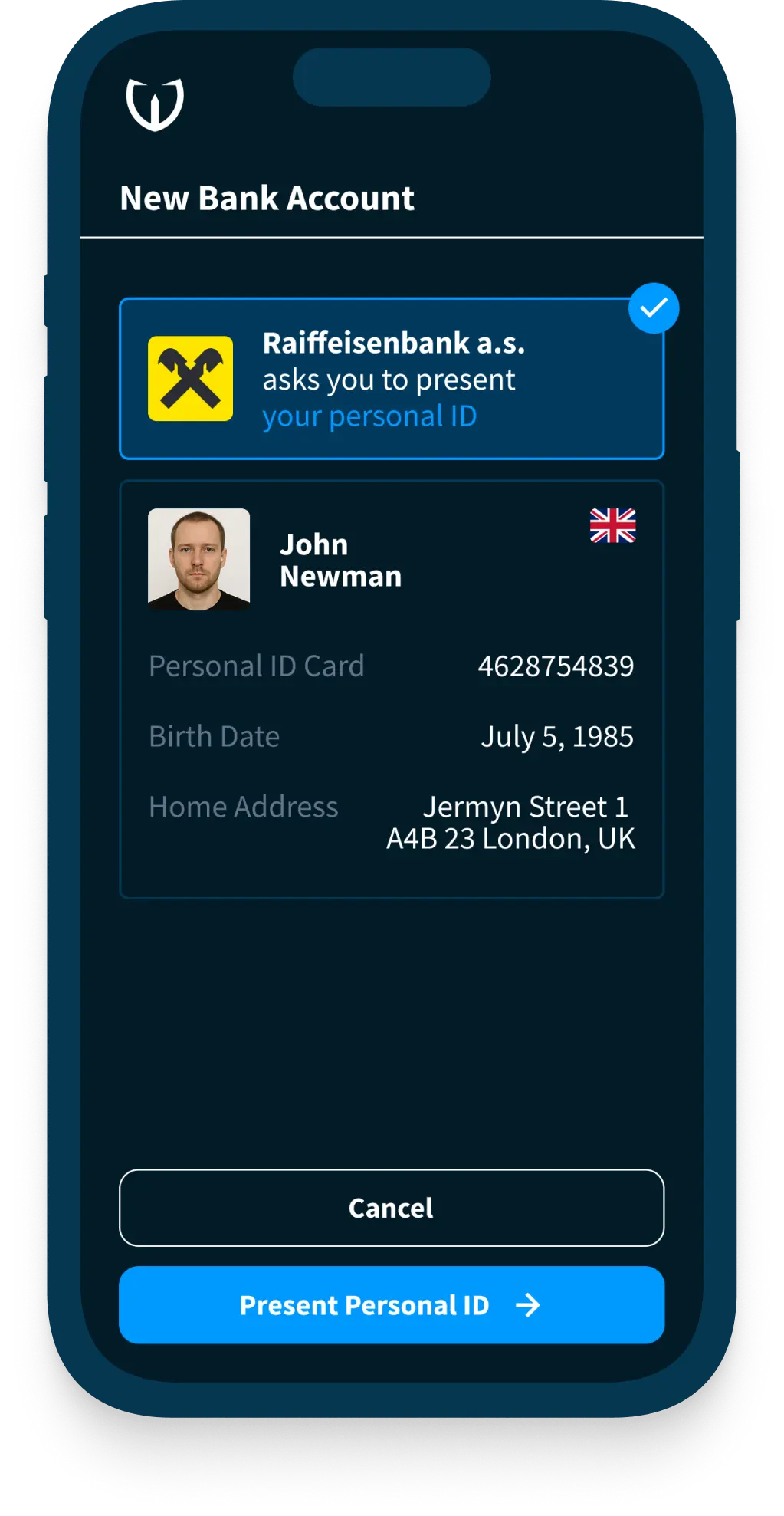
Digital onboarding and KYC
Turn digital IDs into new customers.
Strong Customer Authentication
Quick logins and payment approval.
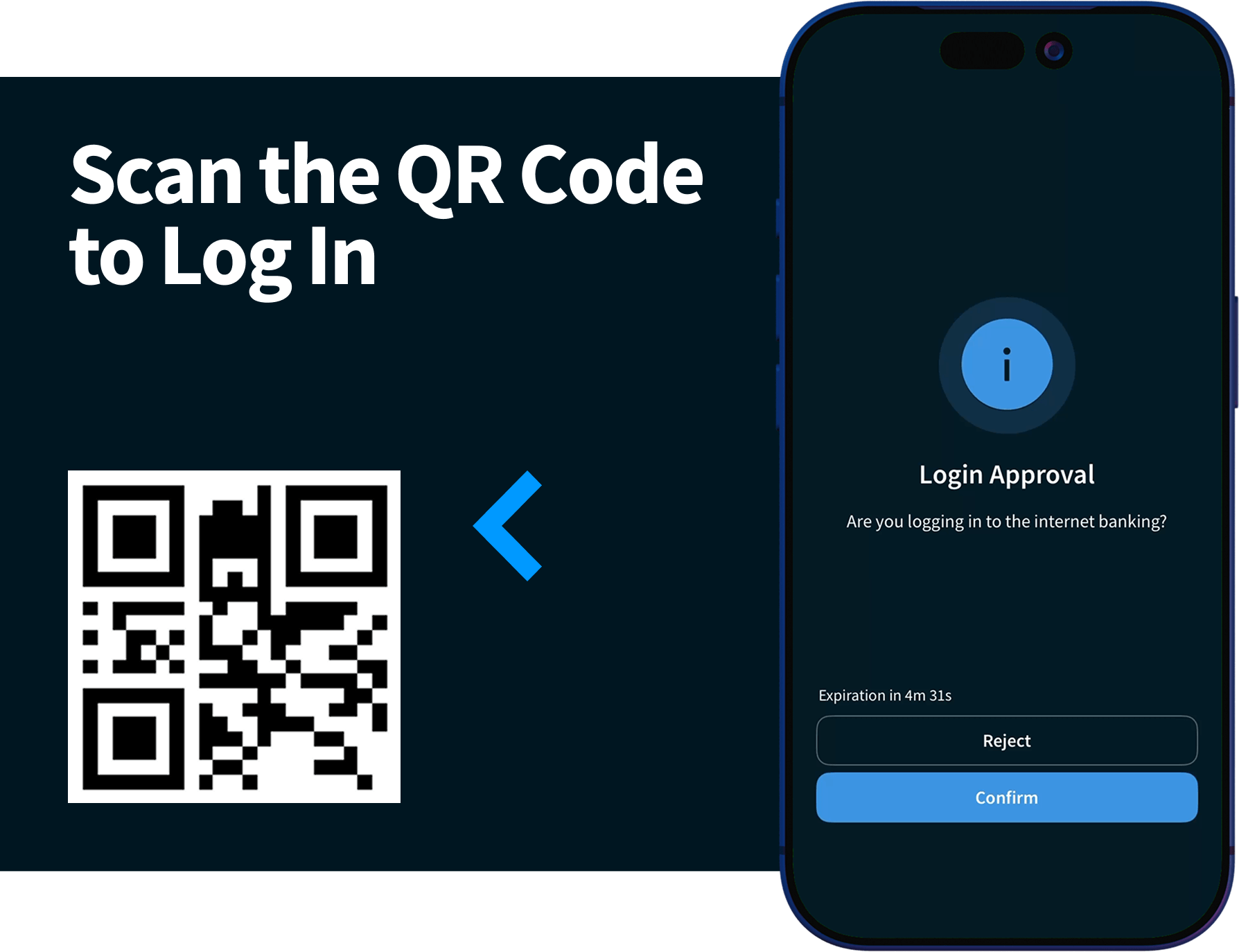
Mobile and web banking login
Fast and secure login with device-bound keys and biometric/PIN verification.
Step-up for high-risk actions
Adaptive flows for password change, device change, profile updates, and account recovery.

Payments and transaction signing
Fast payment approvals via convenient biometric authentication and secure PIN codes.
Features
Features headline
Great to Use
Your customers will love the passwordless experience provided by our solutions.
Quantum-resistant
Under the hood, we use post-quantum cryptography endorsed by NIST.
Lorem ipsum dolor sit amet, consectetur adipisicing elit sed do eiusmod tempor.
Comply with regulations
Policy controls, step-up flows, and evidence generation to support PSD3/PSR SCA requirements and audits.
Reduce account takeover
Bind a user to a mobile device using cryptographic keys stored in platform security (e.g., TEE/SE/Keychain).
Improve user experience
Fast login and payment approvals, convenient biometric authentication, secure PIN code.
Audit and observability
Evidence-rich logs, export capabilities, and monitoring hooks for SIEM/SOC workflows.
Multi-factor authentication
Device biometrics (Face ID) and PIN, device possession, and fallback methods designed for inclusivity and resilience.
Policy-driven authentication
Adaptive rules: step-up, risk thresholds, factor constraints, channel restrictions, and user journeys.
Secure device binding
Prevent common OTP/push weaknesses with device binding, signed approvals, and contextual checks.
Social attack resistance
Mitigate OTP interception, SIM swap exposure, overlay attacks, and social engineering patterns.
Transaction and login approvals
Approve logins and high-risk actions with signed messages and clear user context (who/what/where).
Deployment options
Front-End
Back-End
Front-End
Back-End
Front-End
Back-End
User Device
Back-End
Front-End
Back-End
Back-End
Ready to modernize your authentication?
Get a walkthrough tailored to your user journeys, risk model, and deployment constraints.
