Products
Mobile In‑App Protection
Defend mobile applications from the most advanced cyber attacks and prevent tampering, reverse engineering, malware, and data exfiltration by adding active, in-app protection features.

Comprehensive security
Protect applications against advanced mobile threats and improve resilience.
Fast deployment
Integrate the security suite in 10 minutes with just a few lines of code.
Visualization and insights
Inspect devices and threats across your ecosystem through an online dashboard.
Protect against mobile threats
Prevent, detect, and block attacks targeting your mobile applications.
Support regulatory compliance
Meet strict mobile security standards, including OWASP-aligned requirements.
Gain real-time threat visibility
Monitor devices and security threats across your ecosystem using an analytics dashboard.
Limited in-house expertise and knowledge
Slow response to evolving threats
High effort, limited business impact
Lack of external benchmarking
Integrity protection
Protection against tampering, repackaging, and reverse engineering.
Runtime protection
Device risk scanning and assessment with secure analysis.
Security signals
Threat signals ready to feed into fraud detection systems.
Compliance with standards
OWASP-aligned mobile security and resilience controls.
Online analytics dashboard
On-premise or cloud component for ecosystem-wide visibility.
Smooth integration
Developer-friendly integration with minimal code changes.
Trusted by leading financial organizations



Benefits
Secure your mobile ecosystem end-to-end
Comprehensive security
Protect applications against advanced mobile threats and improve resilience.
Fast deployment
Integrate the security suite in 10 minutes with just a few lines of code.
Visualization and insights
Inspect devices and threats across your ecosystem through an online dashboard.
Protect against mobile threats
Prevent, detect, and block attacks targeting your mobile applications.
Support regulatory compliance
Meet strict mobile security standards, including OWASP-aligned requirements.
Gain real-time threat visibility
Monitor devices and security threats across your ecosystem using an analytics dashboard.
Limited in-house expertise and knowledge
Slow response to evolving threats
High effort, limited business impact
Lack of external benchmarking
Integrity protection
Protection against tampering, repackaging, and reverse engineering.
Runtime protection
Device risk scanning and assessment with secure analysis.
Security signals
Threat signals ready to feed into fraud detection systems.
Compliance with standards
OWASP-aligned mobile security and resilience controls.
Online analytics dashboard
On-premise or cloud component for ecosystem-wide visibility.
Smooth integration
Developer-friendly integration with minimal code changes.
Use Cases
Protect every app, everywhere
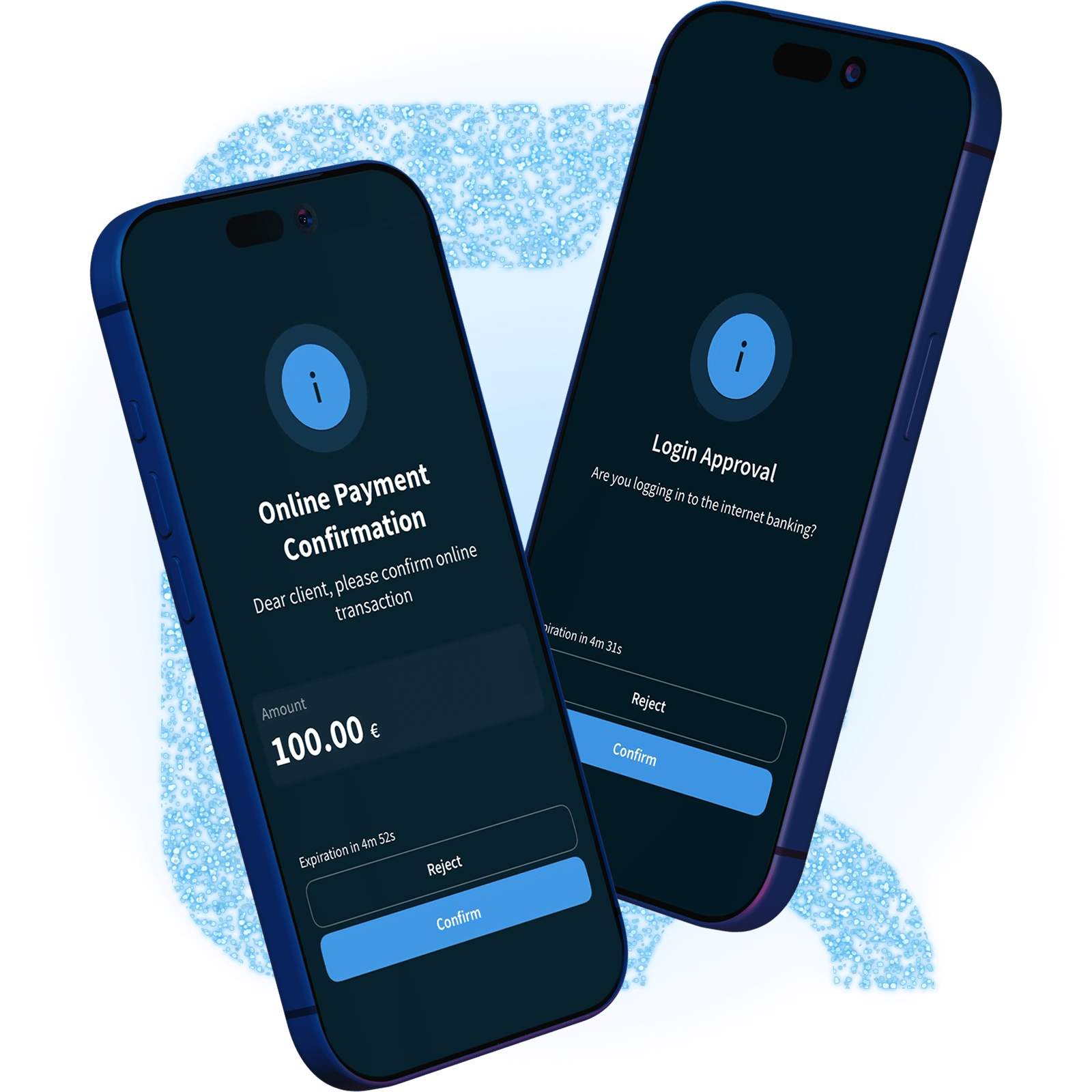
In-App Protection is only as secure as the device it runs on. Our solution assesses device risk through scanning and cloud analysis to help prevent threats, detect suspicious behavior, and block malicious activity.

Prevent
Proactively identify and neutralize threats before they can compromise device security.
Detect
Continuously monitor suspicious behavior and alert to potential security breaches.

Block
Prevent unauthorized access and malicious activity targeting your applications.
Regulations and Standards
Certifications
Where in-house mobile security solutions fail?

Comprehensive security

Fast deployment

Visualization and insights

Protect against mobile threats

Support regulatory compliance

Gain real-time threat visibility

Limited in-house expertise and knowledge

Slow response to evolving threats

High effort, limited business impact

Lack of external benchmarking

Integrity protection

Runtime protection

Security signals

Compliance with standards

Online analytics dashboard

Smooth integration
Case Study
ČSOB strengthens mobile security with Wultra’s in-app protection
Československá obchodní banka (ČSOB), one of the largest and most trusted financial institutions in the Czech Republic, has enhanced the security of its mobile banking app by deploying Wultra’s In-App Protection. Learn how the cloud-based solution proactively protects users against malware threats and device-level attacks while maintaining speed and a seamless user experience.


At ČSOB we are continuously working to strengthen the security of our mobile banking applications. The cloud-based solution from Wultra helped us protect our clients against malware and device-level risks, without compromising the quality of the user experience. Meeting our specific requirements made it easy to integrate the solution into our particular needs

Features
Advanced in-app protection for mobile apps
Built for banking and fintech, the solution enforces mobile app resilience controls directly on the device and sends threat signals to your fraud detection systems.
Comprehensive security
Protect applications against advanced mobile threats and improve resilience.
Fast deployment
Integrate the security suite in 10 minutes with just a few lines of code.
Visualization and insights
Inspect devices and threats across your ecosystem through an online dashboard.
Protect against mobile threats
Prevent, detect, and block attacks targeting your mobile applications.
Support regulatory compliance
Meet strict mobile security standards, including OWASP-aligned requirements.
Gain real-time threat visibility
Monitor devices and security threats across your ecosystem using an analytics dashboard.
Limited in-house expertise and knowledge
Slow response to evolving threats
High effort, limited business impact
Lack of external benchmarking
Integrity protection
Protection against tampering, repackaging, and reverse engineering.
Runtime protection
Device risk scanning and assessment with secure analysis.
Security signals
Threat signals ready to feed into fraud detection systems.
Compliance with standards
OWASP-aligned mobile security and resilience controls.
Online analytics dashboard
On-premise or cloud component for ecosystem-wide visibility.
Smooth integration
Developer-friendly integration with minimal code changes.
Deployment options
Front-End
Back-End
Front-End
Back-End
Front-End
Back-End
User Device
Back-End
Front-End
Back-End
RESOURCES
Commercial Model
Only pay for active users
Our licensing aligns with typical rollout models and supports deployment options for regulated environments.
Related Products
Learn more
Read about trends in mobile application security
Read About Modern Authentication in Banking and Finance
Ready to modernize your authentication?
Get a walkthrough tailored to your user journeys, risk model, and deployment constraints.






.png)
